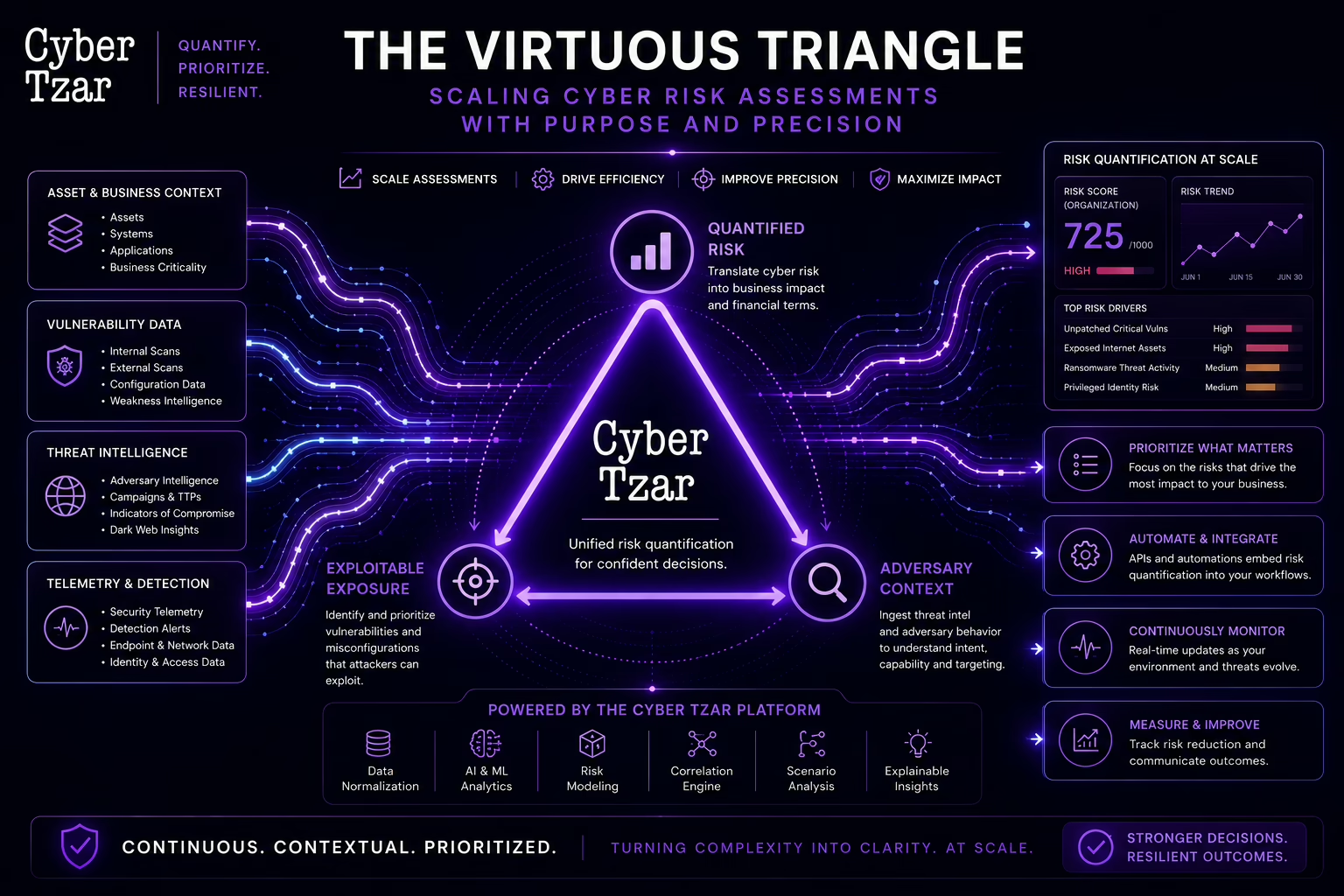
Risk isn’t static. It changes with every new CVE, every new phishing campaign, and every new misconfigured server. In a [...]
The National Cyber Security Centre (NCSC) guidance on Risk Management provides a structured and practical framework for understanding, assessing, and [...]
Introduction: APIs – The Backbone of Modern Startups Startups today rely heavily on APIs (Application Programming Interfaces) to power their [...]
Introduction: Why Cyber Insurance Isn’t a Silver Bullet Cyber insurance is often seen as a safety net for businesses, protecting [...]
Introduction: The Traditional Perimeter Is Dead For decades, cybersecurity in the defence sector relied on perimeter-based security—a “castle-and-moat” approach where [...]
Introduction: The Invisible Risk Lurking in Your Supply Chain Most organisations believe they have control over their IT infrastructure, but [...]