Strengthening Supply Chain Cyber Resilience Across Critical UK Industries Cyber Tzar is proud to announce a new strategic partnership with [...]
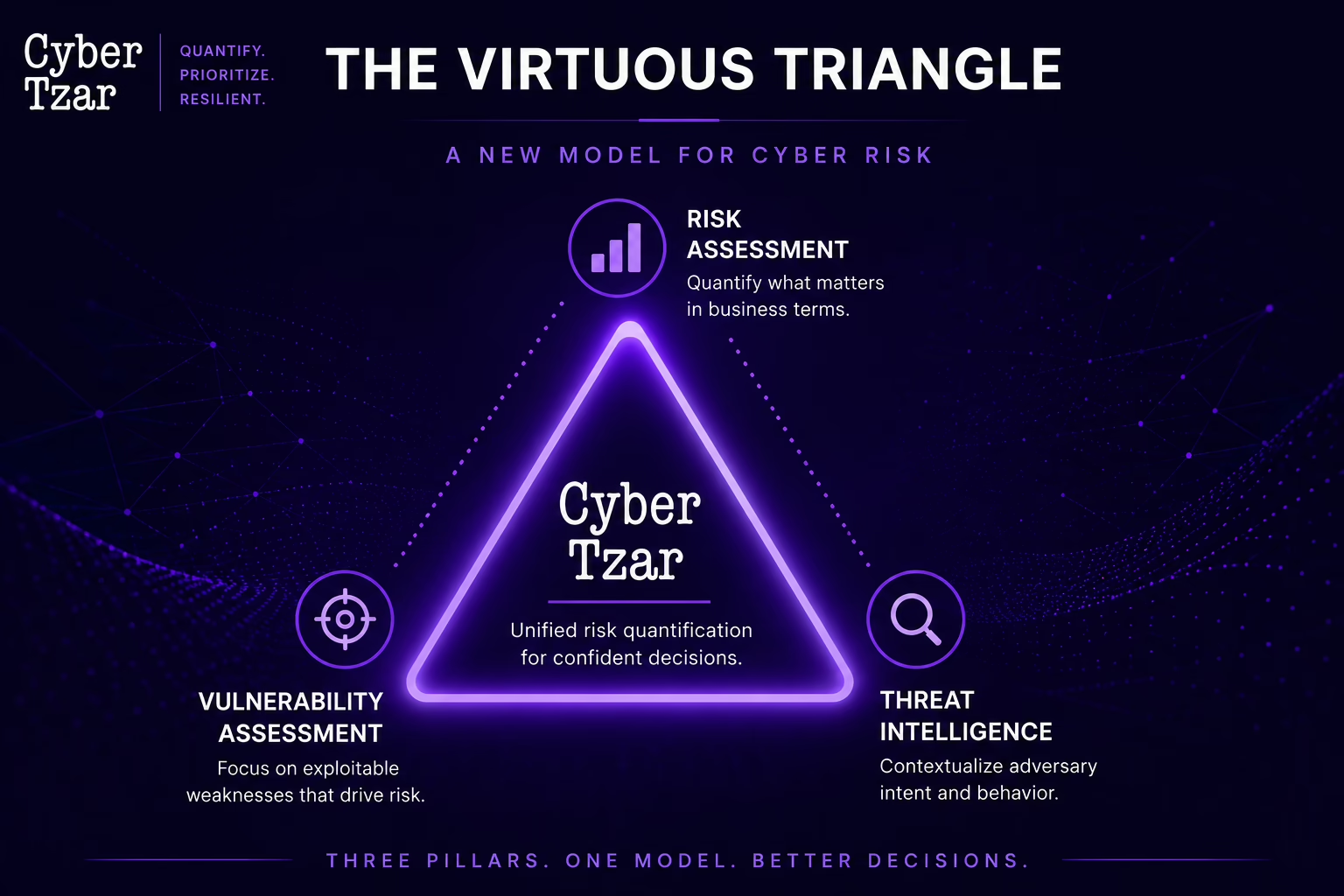
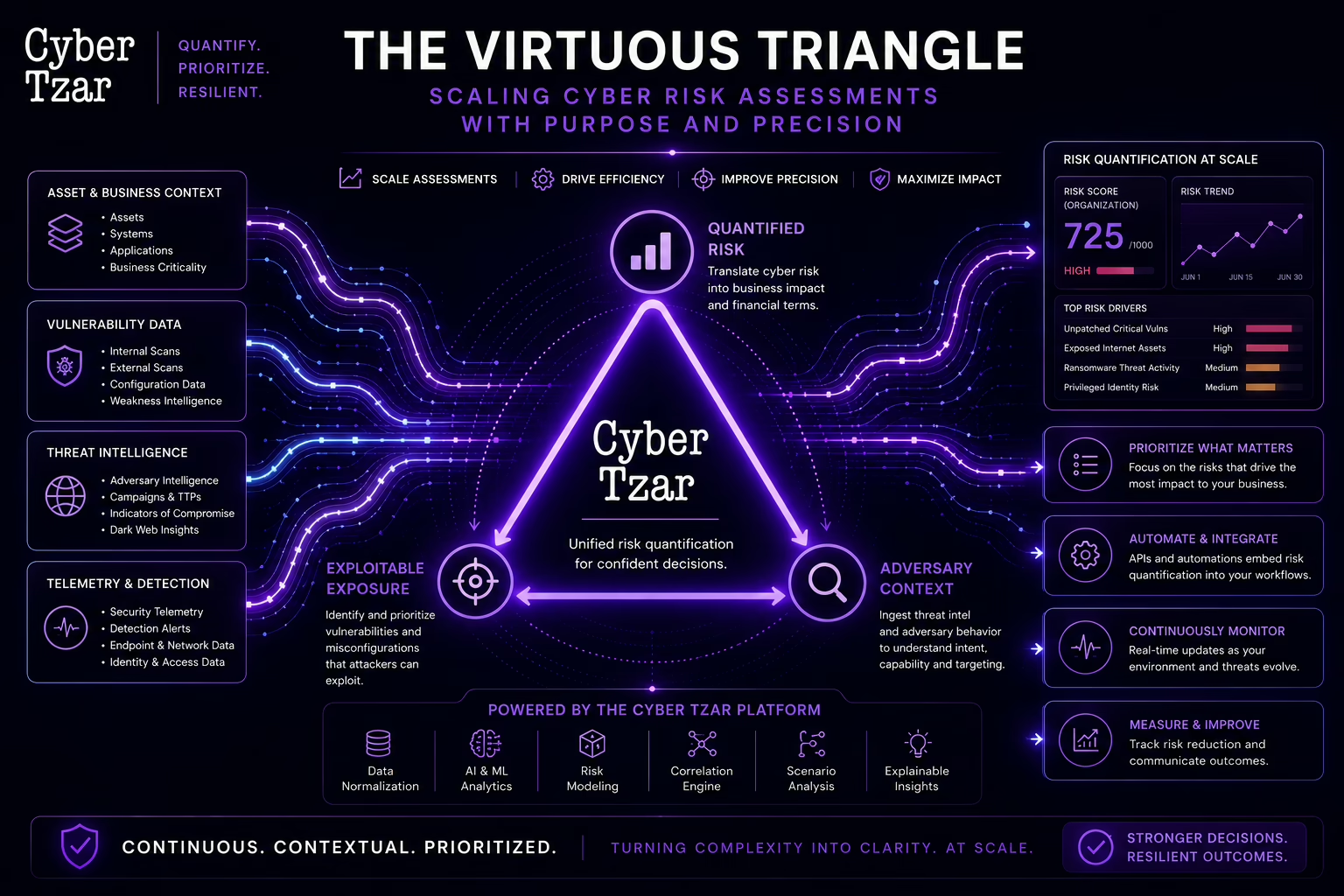
Executive Summary Cyber risk quantification has often been viewed with scepticism, dismissed as simplistic, static, or out of step with [...]
Risk isn’t static. It changes with every new CVE, every new phishing campaign, and every new misconfigured server. In a [...]
As we approach our 100,000th company scan, the Cyber Tzar team is proud — not just because of the milestone [...]
In an interconnected world, organisations increasingly rely on third-party vendors to support operations, deliver services, and drive innovation. However, this [...]
As supply chains become more interconnected, organisations face mounting risks from third-party vendors. IBM’s 2024 Cost of a Data Breach [...]