The beginning of our Journey with NatWest Accelerator Program In the fast-paced world of cybersecurity, staying ahead of the curve [...]
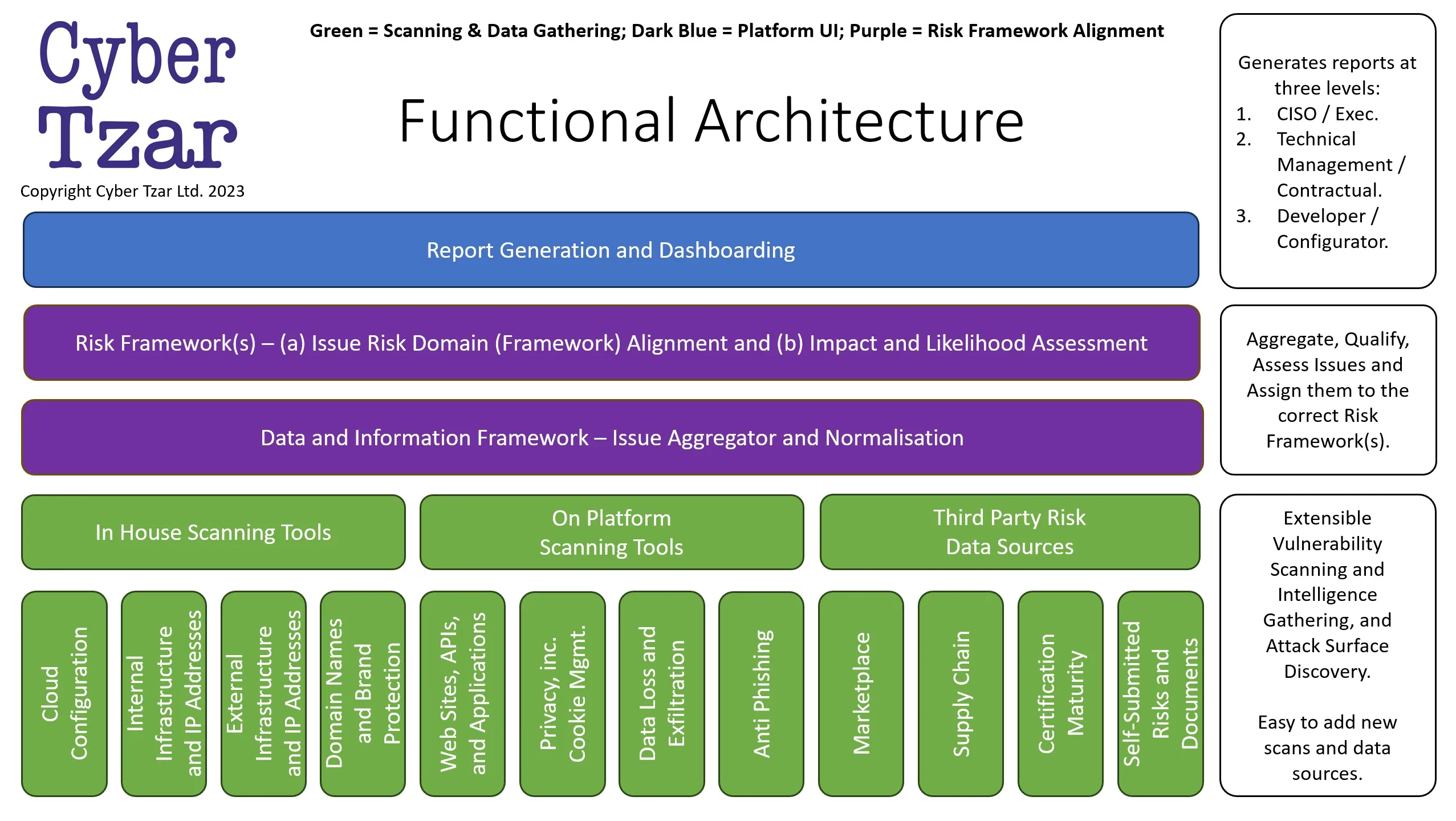
Cyber Tzar Functional Architecture If you’re interested in how the Cyber Tzar Cyber Risk Management platform “works” you’ve come to [...]
Cyber Tzar join the 7th NCSC for Startups programme We are incredibly pleased to be able to share with you [...]
Strengthening Cybersecurity Across Supply Chains: A Breakthrough Solution! In today’s interconnected digital landscape, one thing is crystal clear: cybersecurity isn’t [...]
Cyber Tzar Joins Forces with Chamber of Commerce Future Faces to Empower Young Entrepreneurs In an ever-evolving digital landscape, cybersecurity [...]
Empowering Businesses with a Cutting-Edge Cyber Risk Management Platform In today’s ever-evolving digital landscape, cyber risks pose a significant threat [...]